DoD
Throughout this guide, we break down the deployment and configuration of the DoD policy with the following sections:
Introduction
Anchore Enterprise scans for the following DoD policies:
- DISA Image Creation and Deployment Guide
- IronBank
Being part of the Department of Defense (DoD), Defense Information Systems Administration (DISA) is the agency that provides IT and communications support to both the US government and federal organizations. The DISA Image Creation and Deployment Guide Policy provides security and compliance checks that align with specific NIST 800-53 and NIST 800-190 security controls and requirements as described in the DoD Container Image Creation and Deployment Guide.
Anchore checks for the following control specifications in the DISA policy:
- AC6(10) Container Image Must Have Permissions Removed from Executables that Allow a User to Execute Software at Higher Privileges
- CM-6(b) Confidential Data Checks
- CM-7(1b) Network Port Exposure Checks
- CM-7(a) Container Image Build Content Checks
- IA-5(2a) Base Image Checks
- IA-5(7) Embedded Credentials
- RA-5 Software Vulnerability Checks
- SC-5 Image Checks
- SC-8(2) Base Image Checks
- SI-2(6) Image Software Update/Layer Checks
The DoD IronBank policy validates images against DoD security and compliance requirements in alignment with U.S. Air Force security standards at Platform One and IronBank. The IronBank policy has been written in accordance to the following DoD documentation.
- Dockerfile Checks
- User Checks
- File Checks
- Istio Checks
- Software Checks
- Transfer Protocol Checks
- Node.js Checks
- Etcd Checks
- Snort Checks
- Jenkins Checks
- Grafana Checks
- UBI7 Checks
- Chef Checks
- Sonarqube Checks
- Prometheus Checks
- Postgres Checks
- Nginx Checks
- OpenJDK Checks
- Twistlock Checks
- Keycloak Checks
- Fluentd Checks
- Elasticsearch Checks
- Kibana Checks
- Redis Checks
- Apache HTTP Checks
- Apache Tomcat Checks
Enabling the DoD Policy
For this walkthrough, we will be using the IronBank policy for demonstration.
If you are an Anchore Enterprise customer, you will receive an email, which includes a json file for the IronBank policy that comes with your service.
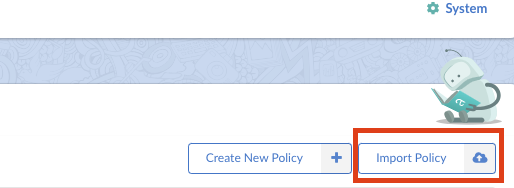
Navigate to the Policies tab in Anchore Enterprise and click on the ‘Import Policy’.
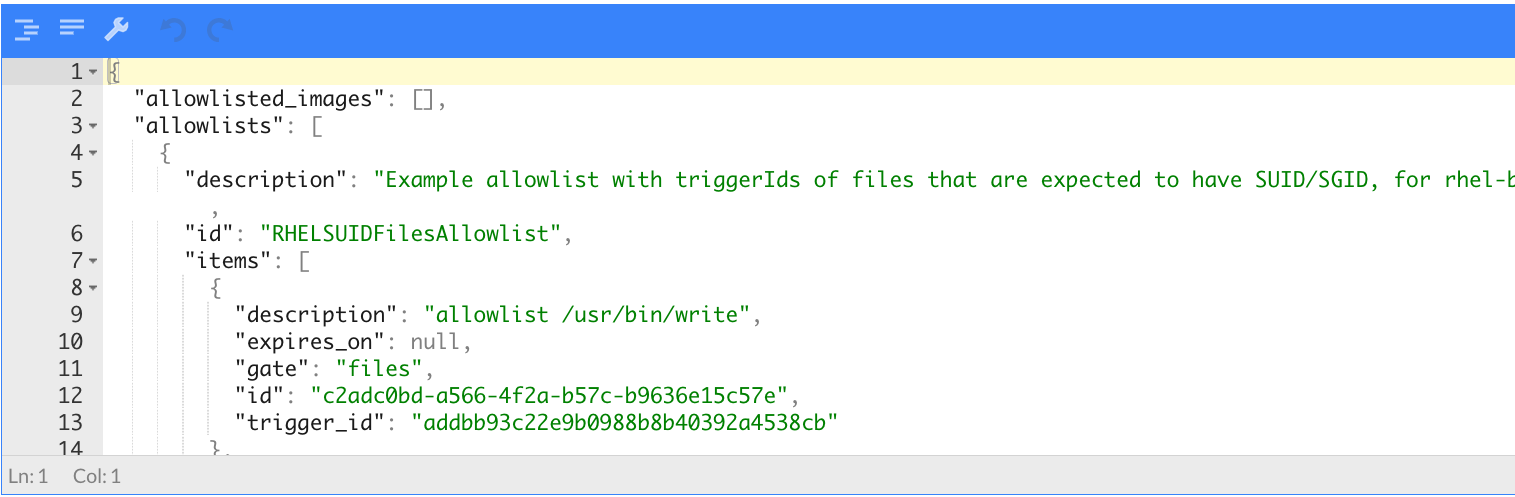
Drag and drop, or paste the .json file to import the policy into Anchore Enterprise.
Or run the following command using AnchoreCTL
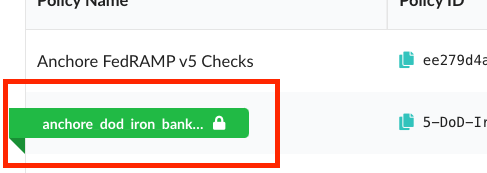
# anchorectl policy add --input anchore_dod_iron_bank_security_policies_09212022.json ✔ Added policy Name: anchore_dod_iron_bank_security_policies_09212022 Policy Id: 5-DoD-Iron-Bank-Docker Active: false Updated: 2024-05-03T21:42:53ZAfter a successful import, the IronBank policy will be available in the Policies tab.
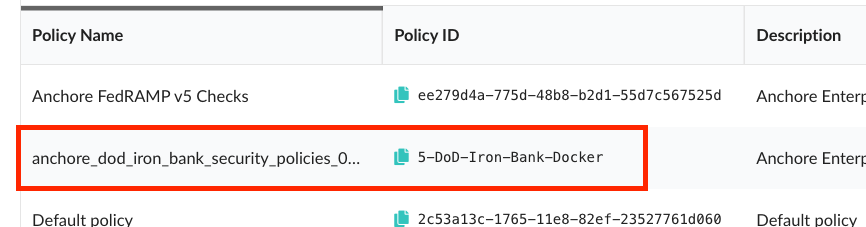
Or run the following command using AnchoreCTL
# anchorectl policy list ✔ Fetched policies ┌──────────────────────────────────────────────────┬──────────────────────────────────────┬────────┬──────────────────────┐ │ NAME │ POLICY ID │ ACTIVE │ UPDATED │ ├──────────────────────────────────────────────────┼──────────────────────────────────────┼────────┼──────────────────────┤ │ Default policy │ 2c53a13c-1765-11e8-82ef-23527761d060 │ true │ 2024-05-03T22:04:08Z │ │ anchore_dod_iron_bank_security_policies_09212022 │ 5-DoD-Iron-Bank-Docker │ false │ 2024-05-03T22:04:08Z │ └──────────────────────────────────────────────────┴──────────────────────────────────────┴────────┴──────────────────────┘In order to activate the IronBank policy, simply click on the circle under ‘Active’.
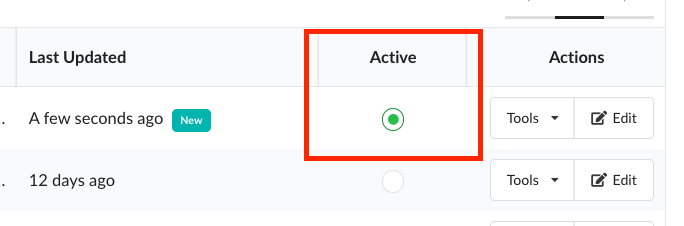
Once activated, you will see that the IronBank policy is highlighted in green.
Or run the following command using AnchoreCTL
# anchorectl policy activate 5-DoD-Iron-Bank-Docker ✔ Activate policy Name: anchore_dod_iron_bank_security_policies_09212022 Policy Id: 5-DoD-Iron-Bank-Docker Active: true Updated: 2024-05-03T22:07:54ZNavigate to the Image tab in Anchore Enterprise and you will now be able to evaluate an image with the IronBank policy.
Or run the following command using AnchoreCTL
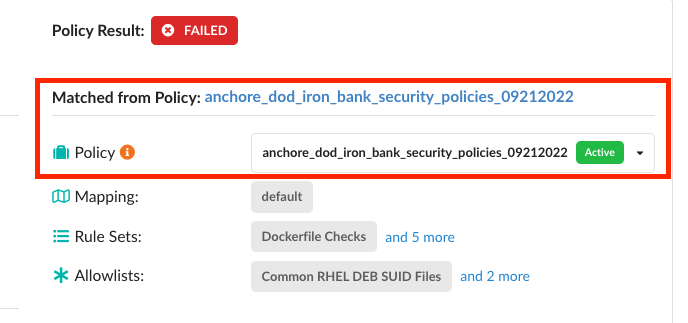
As an example, we will add a centos image and evaluate it using the IronBank policy. please give it some time for Anchore to analyze the image when added
# anchorectl image add docker.io/centos:latest --wait ✔ Added Image docker.io/centos:latest ✔ Analyzed Image docker.io/centos:latest Image: status: analyzed (active) tag: docker.io/centos:latest digest: sha256:a1801b843b1bfaf77c501e7a6d3f709401a1e0c83863037fa3aab063a7fdb9dc id: 5d0da3dc976460b72c77d94c8a1ad043720b0416bfc16c52c45d4847e53fadb6 distro: centos@8 (amd64) layers: 1To apply the active IronBank policy and see all the details of violation:
#anchorectl image check docker.io/centos:latest --detailTo apply the active IronBank policy and get a simple pass/fail check:
#anchorectl image check -f docker.io/centos:latest ✔ Evaluated against policy [failed] docker.io/centos:latest Tag: docker.io/centos:latest Digest: sha256:a1801b843b1bfaf77c501e7a6d3f709401a1e0c83863037fa3aab063a7fdb9dc Policy ID: 5-DoD-Iron-Bank-Docker Last Evaluation: 2024-05-03T22:08:52Z Evaluation: fail Final Action: stop Reason: policy_evaluation
Configuring Rule Sets for the DoD Policy
Some of the control specifications need configuration based on the user’s environment. The control specifications are represented by ‘Rule Sets’ in Anchore Enterprise. Navigate to the Policies tab and click on the ‘Edit’ under ‘Actions’.
It is recommended all configuration changes to rule sets be done in the Anchore Enterprise UI.
The IronBank policy does not need any configuration changes for the Rule Sets. However, the DISA policy will need configuration changes for certain specifications.
As an example, a user may need to change the port configuration for CM-7(1b): Network Port Exposure Checks, which checks for network port exposures.
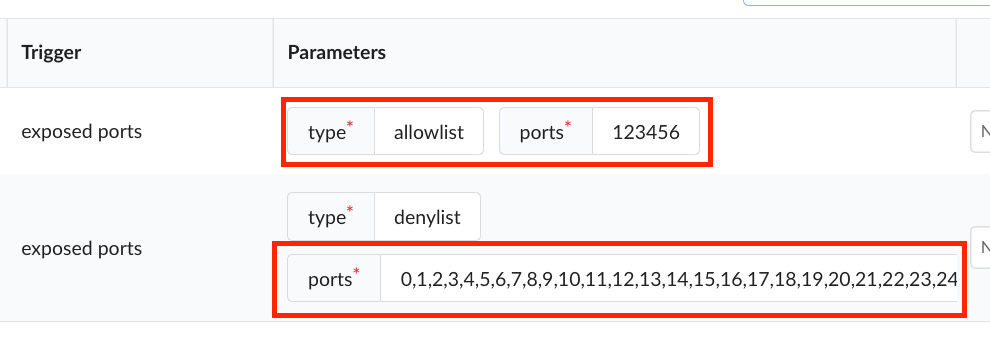
Make sure to go through each of the Rule Sets to configure all applicable specifications. Save and close.
The following rule sets MUST be configured before using the DISA policy pack:
- CM-6(b) Confidential Data Checks
- CM-7(1b) Network Port Exposure Checks
- CM-7(a) Container Image Build Content Checks