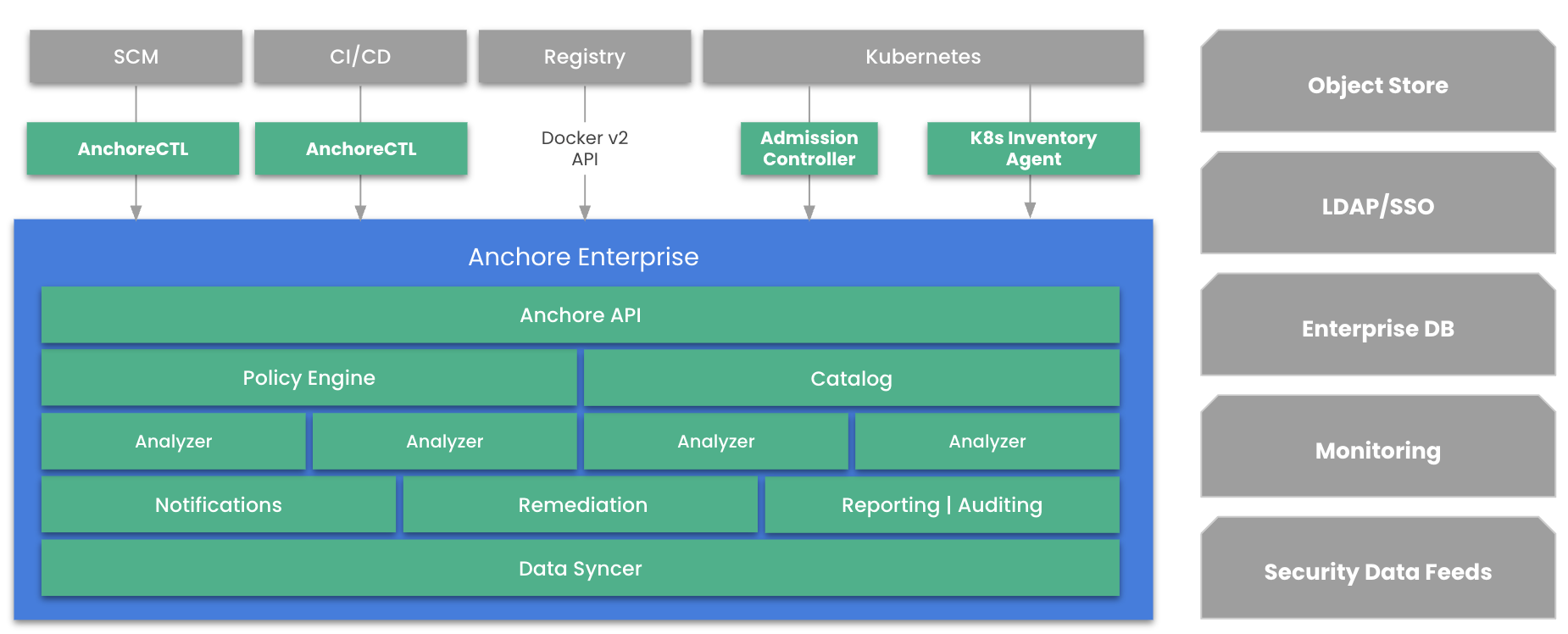
Architecture Overview
Anchore Enterprise is a distributed application deployed as a set of container images that communicate through RESTful APIs and a shared PostgreSQL database. The platform can be deployed on Kubernetes (via Helm), Docker Compose, or as a pre-configured cloud image. Each service runs independently and can be scaled horizontally to meet throughput requirements.
Services
API Service
The API service is the primary external-facing gateway for Anchore Enterprise. All client interactions — from AnchoreCTL, the web UI, and third-party integrations — route through this service. It exposes a RESTful API (v2) that provides access to image management, policy evaluation, vulnerability queries, user and account administration, SBOM operations, reporting, and system configuration.
Catalog
The catalog is the central state manager. It coordinates image lifecycle operations, tracks analysis state, manages subscriptions and event notifications, and provides data access to all other services from the backend PostgreSQL database. The catalog also handles artifact lifecycle policies (automatic archiving and deletion), garbage collection, and Kubernetes runtime inventory tracking.
Analyzer
The analyzer generates SBOMs from container images and source repositories. It unpacks image layers, catalogs all software packages and dependencies, detects malware using ClamAV signatures, searches for embedded secrets, and extracts filesystem metadata. Each analyzer instance processes one artifact at a time; scaling analyzer replicas increases parallel analysis throughput.
In distributed analysis mode, SBOM generation happens locally on the AnchoreCTL client and the resulting SBOM is uploaded to Anchore Enterprise for evaluation — bypassing the need for the analyzer to pull images directly.
Policy Engine
The policy engine loads SBOMs and evaluates them against the configured policy rules. It uses a gate-and-trigger model where each gate (vulnerabilities, licenses, secrets, file permissions, metadata) contains triggers with configurable parameters. The policy engine also handles vulnerability matching, applying the precision matching algorithm against the appropriate data feeds, and incorporates EPSS scores and KEV status into results. Policy evaluation results are stored and returned as pass, warn, or fail outcomes.
Data Syncer
The data syncer periodically downloads and normalizes datasets from the hosted Anchore Data Service. These datasets include vulnerability databases from 20+ sources, CISA KEV annotations, EPSS exploit prediction scores, ClamAV malware signatures, and STIG compliance profiles. By default, the data syncer checks for updates hourly. In air-gapped deployments, data synchronization is performed manually using AnchoreCTL.
Reports and Reports Worker
The reports service provides a GraphQL-based API for querying vulnerability, policy, and inventory data across the deployment. Users can create, schedule, and export reports in CSV or JSON format. The reports worker handles asynchronous report generation and scheduled report execution in the background.
Notifications
The notifications service manages event-driven alerts. When analysis completes, policy evaluations change, or vulnerability states are updated, the notification service delivers alerts through configurable endpoints including webhooks, Slack, Jira, and email. Notifications can be filtered using selectors to route specific event types to specific destinations.
SimpleQueue
The SimpleQueue is a PostgreSQL-backed internal task queue used by other services for asynchronous task distribution, worker coordination, and background job processing.
Clients
AnchoreCTL
AnchoreCTL is the Go-based command-line tool for Anchore Enterprise. It provides 100+ commands covering image analysis, policy evaluation, vulnerability scanning, SBOM management, feed synchronization, user administration, and system operations. AnchoreCTL includes an embedded Syft library for local SBOM generation, enabling distributed analysis without requiring the server to pull images. It supports multiple output formats including text tables, JSON, YAML, CSV, and HTML.
Anchore Enterprise Web UI
The web UI provides a browser-based interface for managing images, creating and editing policies, viewing vulnerabilities, generating reports, configuring notifications, managing user accounts and registries, and monitoring system health. It also offers WYSIWYG configuration for custom login messages, banners, and links.
Integrations
Kubernetes Admission Controller
The Kubernetes Admission Controller intercepts image deployments and evaluates them against Anchore Enterprise policies before allowing them into the cluster. Images that fail policy evaluation can be blocked, providing a runtime enforcement point.
Kubernetes and ECS Runtime Inventory
The Kubernetes Inventory Agent (anchore-k8s-inventory) and ECS Inventory Agent (anchore-ecs-inventory) run inside runtime environments and continuously report the container images in use back to Anchore Enterprise. This enables ongoing vulnerability monitoring and policy compliance checking of live workloads.
Multi-Tenancy
Accounts
Accounts provide data isolation boundaries within Anchore Enterprise. Each account has its own images, SBOMs, policies, notifications, and users. Accounts can be mapped to teams, projects, or applications. Cross-account access is available for administrative users.
Users and RBAC
Users belong to accounts and are assigned roles through role-based access control (RBAC). Anchore Enterprise supports local authentication with hashed passwords (Argon2), OAuth2 token-based authentication, SAML2 SSO, and API key authentication. Usernames are unique across the deployment to enable direct API authentication.