Anchore Data Service
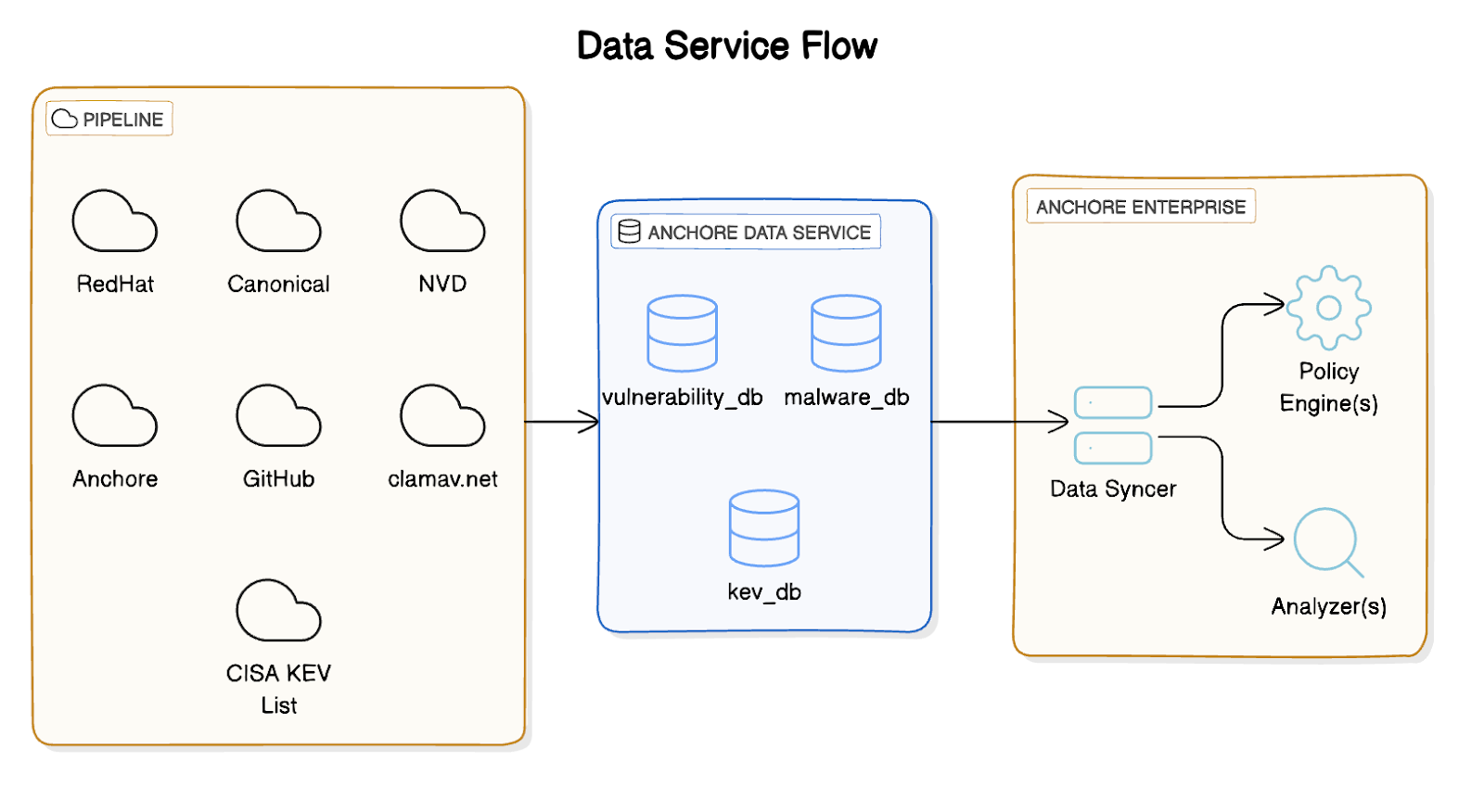
Anchore Enterprise relies on external vulnerability and security data to perform accurate analysis. The Anchore Data Service is a hosted service operated by Anchore that aggregates, normalizes, and serves pre-built datasets to customer deployments. Authentication is handled automatically through your Anchore Enterprise license — no additional credentials are required.
Datasets
The Anchore Data Service currently provides the following datasets. Upstream pipelines refresh these datasets every 6 hours, and each Anchore Enterprise deployment polls for updates hourly by default (configurable via the Data Syncer service).
Vulnerability Database
The vulnerability database (vulnerability_db) contains vulnerability records aggregated from 20+ sources, including:
- NVD (National Vulnerability Database), with additional data enrichment by Anchore
- GitHub Security Advisories (GHSA)
- RHEL (Red Hat Enterprise Linux)
- Debian
- Ubuntu
- Alpine
- Amazon Linux
- Oracle Linux
- SLES (SUSE Linux Enterprise Server)
- Fedora
- Arch Linux
- Mariner / Azure Linux
- VMware PhotonOS
- Wolfi
- Chainguard (Libraries and OS)
- Bitnami
- MSRC (Microsoft Security Response Center)
- Echo
- MinimOS
- SecureOS
Vulnerability Match Exclusions
The vulnerability match exclusions database (vulnerability_match_exclusions_db) contains CVEs that Anchore has identified as false positives and excluded from matching. This is an Anchore Enterprise-exclusive dataset — it is manually curated by Anchore and is not included in the open-source Grype vulnerability data, providing noise reduction beyond what public feeds offer.
EPSS and KEV Data
Vulnerability records are enriched with:
- EPSS (Exploit Prediction Scoring System) scores and percentiles, providing a probability estimate of exploitation in the wild
- CISA KEV (Known Exploited Vulnerabilities) annotations, flagging vulnerabilities with confirmed active exploitation
ClamAV Malware Database
The malware database (clamav_db) contains ClamAV signatures used to detect malware, cryptominers, and other malicious content within container image layers during analysis.
STIG Profiles
The STIG profiles database (stig_profile_db) contains Anchore-supported DISA STIG profiles for evaluating container image compliance against Security Technical Implementation Guides.
Data Syncer Service
Anchore Enterprise includes a Data Syncer service that is responsible for downloading datasets from the Anchore Data Service and making them available to the rest of the deployment. The Data Syncer runs on a configurable schedule (hourly by default) and manages the full lifecycle of dataset synchronization. It communicates with the Anchore Data Service at https://data.anchore-enterprise.com, which must be reachable from your deployment — see Data Syncer Service Configuration for network requirements.
Air-Gapped Deployments
For environments without internet connectivity, datasets can be downloaded externally using AnchoreCTL and then uploaded to the air-gapped deployment. See Air-Gapped Configuration for instructions.
For information on the hosted service status, see the Anchore Data Service Status Page.
To learn more about configuring the Data Syncer, see Data Syncer Service Configuration.
Last modified April 29, 2026